Natsar Cybersecurity Insights
- Mar 27
Comparing DOH and DEC Cybersecurity Requirements for New York’s Water Sector
- Josh Moulin
- Cybersecurity, Compliance & Legal
- 0 comments
Subscribe To Get Notified of New Content!
Your information stays with Natsar—we never sell it or share it.
Intended Audience: Small and mid-sized municipal water and wastewater utilities, along with operators, managers, and local government leaders in New York who will soon be required to comply with the new DOH and DEC cybersecurity regulations.
Editor’s Note (April 2026): Since this article’s original publication, New York’s water and wastewater cybersecurity regulations are no longer just proposed—they have been officially enacted. The DEC formally adopted its rules on March 11, 2026. While the comparative analysis below remains highly accurate, please note that the final deadline for the core DEC controls is now definitively set for March 11, 2027.
Cybersecurity in the water sector is no longer optional—it’s required. Two New York state agencies, the Department of Health (DOH) and the Department of Environmental Conservation (DEC), have each proposed enforceable cybersecurity regulations for drinking water and wastewater systems across New York.
If you manage or operate a community water system or Publicly Owned Treatment Works (POTW), these rules directly affect you.
This post breaks down each rule, clarifies when requirements take effect, and shows how local partners like Natsar can help you meet compliance without the overhead of national consulting firms.
Whether you serve a small rural community or a large regional system, understanding both sets of rules now will save you time, stress, and budget later.
Compliance Timelines at a Glance
New York’s new cybersecurity rules for water and wastewater systems follow a two-phase implementation: certain requirements take effect immediately once the regulations are adopted, while others have delayed deadlines to allow utilities time to plan and implement.
For drinking water systems regulated by the Department of Health (DOH), several obligations are effective right away:
Certified water operators must complete cybersecurity training under Section 5-E.7.
Systems must report any cybersecurity incidents within 24 hours of discovery, per Section 5-E.9.
Vulnerabilities identified in a Cybersecurity Vulnerability Analysis (CVA) must be reported to DOH within 48 hours of identification (Section 5-E.5).
All other cybersecurity requirements outlined in Appendix 5-E must be implemented by January 1, 2027, giving covered water systems time to build or enhance their cybersecurity programs before enforcement begins.
For wastewater systems regulated by the Department of Environmental Conservation (DEC), some requirements also take effect immediately:
Systems must report cybersecurity incidents—orally within 24 hours and in writing within 30 days—as required by Section 750-2.7(h).
The new confidentiality provisions under Section 616.7 protect sensitive cybersecurity information shared with DEC.
The more complex technical and programmatic controls under Section 750-2.9 will take effect one year after the Notice of Adoption is published. In addition, operator cybersecurity training requirements apply to all certifications that expire on or after January 1, 2027, aligning closely with DOH’s compliance timeline.
DOH Cybersecurity Requirements for Drinking Water Systems
The DOH rule (I.D. No. HLT-28-25-00012-P) amends Subpart 5-1 of Title 10 NYCRR to require enforceable cybersecurity controls for community water systems serving more than 3,300 people.
Scope and Key Requirements
Cybersecurity Vulnerability Analysis (CVA): Conduct annually and within 30 days of major infrastructure changes; the CVA must inform the system’s overall cybersecurity program.
Vulnerability Reporting: Report any vulnerabilities identified in the CVA that may impact compliance within 48 hours of discovery.
Incident Reporting: Notify DOH of confirmed cybersecurity incidents within 24 hours of determination.
Operator Training: Certified operators must complete 1 hour of cybersecurity training every 3 years.
Large System Monitoring Threshold: Systems serving > 50,000 people must log and retain network activity for 3 years unless protected by unidirectional devices or isolated networks.
Full Compliance Date: All remaining Appendix 5-E requirements take effect January 1, 2027.
DEC Cybersecurity Requirements for Wastewater Systems
The DEC rule (6 NYCRR Parts 616, 650, and 750) establishes cybersecurity standards for POTWs, focusing on safeguarding operational technology and critical data.
Scope and Key Requirements
Monitoring Threshold: Applies to POTWs with design flow ≥ 10 million gallons per day (MGD). Exceptions apply when only unidirectional connections exist between Operational Technology (OT) and Information Technology (IT)/external networks.
-
Operator Training:
Grades 1/1A and 2/2A → 2 hours every 5 years
Grades 3/3A and 4/4A → 4 hours every 5 years
(No increase in total required training hours — cybersecurity hours are reallocated.)
Incident Reporting: State Pollutant Discharge Elimination System (SPDES) permittees must report cybersecurity incidents orally within 24 hours and in writing within 30 days.
Confidentiality Provision: Cybersecurity information is protected from public disclosure (§ 616.7).
Full Implementation: Core controls (§ 750-2.9) take effect one year after the Notice of Adoption.
Training Compliance: Cybersecurity training hours must be completed for operator certifications expiring on or after January 1, 2027.
Cost and Feasibility Considerations
Both agencies acknowledge that compliance requires investment—but they also allow for flexibility.
Low or No-Cost Alternatives: DEC explicitly permits utilities to leverage free federal or state resources for cyber controls and risk assessments.
-
Estimated Annual Costs:
Small POTWs (1 – 10 employees): $0 – $15K/year
Medium POTWs (10 – 100 employees): up to ≈ $94K/year
(High estimates assume purchase of premium commercial tools for every control — most systems will spend far less.)
Consultant and MSP Options: Both rules allow compliance via existing staff, new hires, or outside consultants — validating the role of partners like Natsar.
Benefit vs. Cost: With the average public-sector data breach costing ≈ $2.6 million, compliance investments offer strong risk reduction ROI.
Immediate Action Required
All regulated entities should begin preparing for these immediate obligations now:
Incident Reporting: Develop clear processes for 24-hour (oral and/or written) incident notifications.
Operator Training: Schedule cybersecurity training that meets DOH and DEC requirements.
Vulnerability Reporting (DOH only): Establish a process for reporting CVA findings within 48 hours.
Even before the 2027 deadlines, these early requirements are in effect as soon as the rules are adopted.
Comparison at a Glance
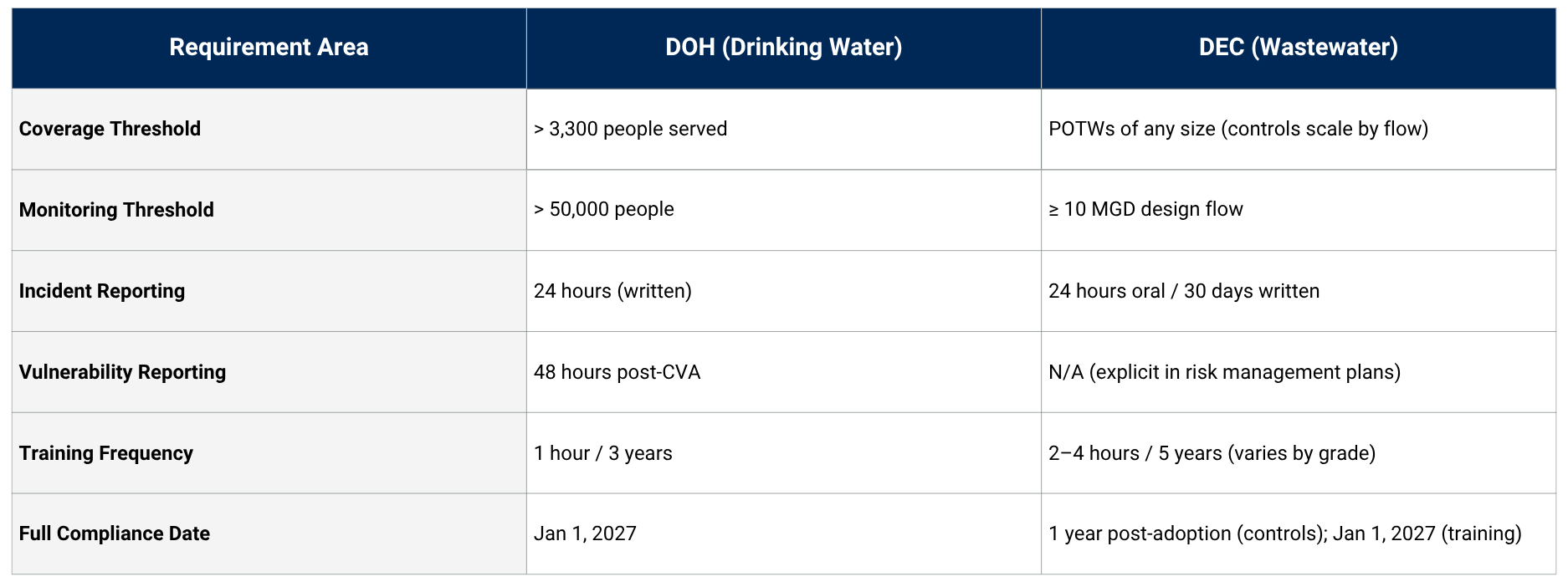
Chart comparing the proposed cybersecurity regulations between DOH and DEC
How Natsar Can Help
As a New York Capital Region-based cybersecurity firm, Natsar brings unmatched public-sector experience and practical expertise to help utilities meet the state’s new cybersecurity mandates efficiently and affordably.
With deep roots in government cybersecurity—including leadership of the Multi-State Information Sharing and Analysis Center (MS-ISAC) while at the Center for Internet Security (CIS)—Natsar’s principal understands firsthand how state and local entities build resilience, manage incidents, and meet compliance under pressure.
Where state agencies stop at assessments and templates, Natsar goes further:
Conducting customized Cybersecurity Vulnerability Analyses (CVAs)
Designing and testing Incident Response Plans (IRPs) and Emergency Response Plans (ERPs)
Delivering operator training and tabletop exercises
Implementing security controls and network defenses based on each utility’s unique risk profile
Choosing a local partner means working with experts who understand New York’s water sector — and who can help you meet state mandates efficiently and confidently.
💧 Let’s get started.
Schedule a consultation with Natsar to get a personalized roadmap for meeting New York’s cybersecurity requirements on time and within budget.
What’s Next
This post outlined the key similarities and differences between the proposed cybersecurity regulations from the New York State Department of Health (DOH) and the Department of Environmental Conservation (DEC).
In our next article, we’ll look at what these new requirements mean in practice—covering implementation timelines, resource challenges, and cost considerations, as well as practical steps utilities can take right now to prepare.
→ Read Part 3: Getting Ready for New York’s Water Cybersecurity Rules
Subscribe to Natsar's Blog for more practical guidance, expert tips, and resources.If you found this helpful, please share your thoughts in the comments section. Your engagement guides future content!